IBM Blockchain Interview Questions for freshers and experienced :-
1. Why is Blockchain a trusted approach?
- Blockchain can be trusted due to so many reasons.
- Its compatibility with other business applications due to its open-source nature.
- Its security. As it was meant for online transactions, the developers have paid special attention to keeping up the pace when it comes to its security.
- It really doesn’t matter what type of business one owns, Blockchain can easily be considered.
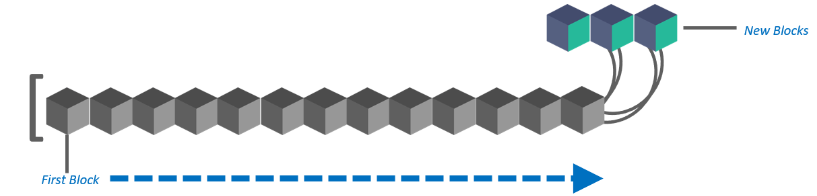
2. What Do You Mean By Blocks In The Blockchain Technology?
Blockchain consists of information of all the financial transactions. A block is nothing but just a list of records. When these lists are combined with each other, they are known as blockchain. For example- an organization has 100 ledger books the combination of which is known as Blockchain and a single ledger would be considered as a block.
3. Why Blockchain Is A Trusted Approach?
Blockchain can be trusted due to so many reasons. The very first one is its compatibility with other business applications due to its open-source nature. Second is its security. As it was meant for online transactions, the developers have paid special attention in keeping up the pace when it comes to its security. It really doesn’t matter what type of business one owns, Blockchain can easily be considered.
4. Is It Possible In Blockchain To Remove One Or More Block From The Networks?
Yes, it can be done. There are times when only a specific portion of this online ledger is to be considered. With the help of default options and filters, this can easily be done without making a lot of efforts.
5. What Do You Know About Blockchain?
Well, it’s a technology which was actually designed for the Bitcoin and later it got a lot of publicity due diverse array of benefits it brings when it comes to monitoring and recording all the financial transactions that are made on a network. It’s a trusted approach and there are a lot of organizations in the present scenario which are using it. As everything is secure, and because it’s an open source approach, it can easily be trusted for the long run.
6. How Does A Block Is Recognized In The Blockchain Approach?
Every block in this online ledger basically consists of a hash pointer which acts as a link to the block which is prior to it, transaction data and in fact a stamp of time.

7. Is There Any Network Specific Conditions For Using Blockchain Technology In An Organization?
There is no specific condition on using it. However, the network must be a peer-to-peer network under the concerned protocols. It actually validates the new block simply and helps organizations to keep up the pace in this matter without investing in third-party applications.
8. What Is Encryption? What Is Its Role In Blockchain?
Data security always matters. Encryption is basically an approach that helps organizations to keep their data secure. In this technique, the data is encoded or changed up to some extent before it is sent out of a network by the sender. The only receiver can understand how to decode the same. In Blockchain, this approach is useful because it simply adds more to the overall security and authenticity of blocks and help to keep them secure.
9. Is It Possible To Modify The Data Once It Is Written In A Block?
No, it is not possible to do so. In case any modification is required, the organization simply has to erase the information from all other blocks too. It is because of no other reason than this, data must be given the extreme care of while using this approach.
10. What Type Of Records Can Be Kept In Blockchain? Is There Any Restriction On Same?
There is no restriction of keeping records of any type in the Blockchain approach. Presently, a lot of organizations all over the world are using this approach and the fact is records of medical transactions, events related to organizations, management activities, transaction processing, identity management, as well as documentation are the common type of records that can be kept on them. It must be noted that the record keeping is not just limited to these applications only.
11. What Is Double Spending?
It is one of the major problems that are associated with the digital cash. In fact, it’s a condition when one digital token is spent multiple times because the token generally consists of a digital file that can easily be cloned. It simply leads to inflation and organizations has to bear a huge loss. One of the primary aims of Blockchain technology is to eliminate this approach up to the possible extent.
12. Explain The Significance Of Blind Signature And How It Is Useful?
It is actually a form of digital signature and in fact an important part of the cryptography in which all the information is made blind before it is actually considered or signed. This is verified approach and is generally considered in the privacy-related protocols where both the author and the signing parties are different. One of the most common examples is digital cash scheme.
13. What Is Secret Sharing? Does It Have Any Benefit In Blockchain Technology?
It is a well-known fact that security matters a lot in digital transactions. Secret sharing is an approach meant for same. In Blockchain technology it is an approach that divides secret or personal information into different units and sent them to the users on the network. The original information can only be combined when a participant to whom a share of the secret is allocated agree to combine them together with others. There are several security-related benefits it can offer in Blockchain technology.
14. What Exactly Do You Know About Executive Accounting? Does Blockchain Support The Same?
Executive accounting is nothing but a special type of accounting which is designed exclusively for a business that offers services to the people. There is no strict upper limit on services and a business can manage any through the executive accounting. Blockchain has algorithms that are specially meant to handle executive accounting. In fact, it cut down many problems that are associated with the same.
15. What Are The Benefits Of Blockchain That You Know?
It encourages secure online transactions which is one of its biggest benefits. Basically, being a distributed and decentralized ledger that keeps a close eye on all the transaction records, it doesn’t let the record to be altered by anyone. This enhances the security. In addition to this, participants and the business owners can always make sure of los cost auditing at the end. One thing that can always be assured with blockchain is every block or unit can be transferred only once which simply eliminates the double spending problem.
16. Name The Two Types Of Records That Are Present In The Blockchain Database?
These records are block records and transactional records. Both these records can easily be accessed and the best thing is it is possible to integrate them each other without following the complex algorithms.
17. What Are The Threads To The Information You Are Familiar With?
There are lots of threats to information in the present scenario. Due to increase in online transactions over the internet, many hackers have become active and are adopting new approaches to hack information and servers that contain financial information. The major threat is software attack, identity theft, information extortion, as well as sabotage. In addition to this, Trojan horses, worms, and viruses are other trouble creators.
18. What Challenges Information Leak Can Impose Of An Organization?
Information leak can cut down the reputation of an organization up to an excellent extent. In addition to this, it can be the reason of organization bearing huge losses. Many organizations who fail to implement security protocols to keep their data secure have already lost the trust of their customers and are struggling very hard to get the same reputation again. The overall profits of any organization can reduce up to 80% if no attention is paid to the online transaction security.
19. Name Organizations That Can Use Blockchain Technology?
There is no strict upper limit on the category of business who can consider this approach. The fact is almost all the businesses are engaged in online or financial transactions that they need to make to run the processes smoothly. Large scale corporations, financial institutions, private businesses, government departments and even defense organizations can trust this technology very easily.
20. What Is Information Processing According To You? What Are The Key Challenges That Are Associated With It?
The information is often shared on a network. Before actually transmitting it over a network, it needs to be changed into formats that can fit the standards of the channels (channel is a link between sender and a receiver). The work done to convert the information at both sender and receiver end is generally regarded as information processing. The biggest challenge to information processing is securing it during that time. Another challenge is processing bulk information can impose a limit on performance.
21. What Does Bip Stands For?
It means Bitcoin improvement proposal.
22. What Are The Key Principles In Blockchain That Are Helpful In Eliminating The Security Threats That Needs To Be Followed?
Yes there are a few principles that need to be followed with respect to time.
They are:
- Auditing
- Securing applications
- Securing testing and similar approaches
- Database security
- Continuity planning
- Digital workforce training
- All these principles are basic and are easy to implement. They are helpful in making the transactions records useful.
23. What Is The Principle On Which Blockchain Technology Is Based On?
It enables the information to be distributed among the users without being copied.
24. Is Blockchain An Incorruptible Ledger?
As per the developer’s claim, the blockchain ledger cannot be corrupted.
25. What Is A Security Policy?
A security policy defines what exactly needs to be secured on a system. It bounds a network user under some core protocols that they all must agree and follow to enhance the overall security. When it comes to information or financial records of an organization, multiple security policies are implemented than just one.
26. How You Will Handle The Risk Management When It Comes To Securing The Transactions Records?
It is basically a process of finding the threats and all the vulnerabilities to the financial records of an organization. The best thing that can be done against this approach is to take the right counter measures against them immediately. Another approach is to pay attention to a back-up plan. Based on the value of information, more approaches such as buying new risk management software can simply be considered. The prime risk to information is from black-hat hackers.
27. Name The Common Type Of Ledgers That Can Be Considered By Users In Blockchain?
These are:
- Centralized Ledgers
- Decentralized Ledgers
- Distributed Ledgers
28. How A Blockchain Ledger Is Different From An Ordinary One?
The first and in fact the prime difference is Blockchain is a digital ledger that can be decentralized very easily. The chances of error in this approach are far less than that in an ordinary ledger. An ordinary ledger is what that is prepared with hands or by human efforts while the Blockchain performs all its tasks automatically. You just need to configure it in a proper manner and by following all the guidelines.
29. A Distributed Digital Ledger Is Used For Recording Transaction In Blockchain. What Does The System Rely On?
It rely on the network nodes.
30. What are the different types of Blockchains?
Blockchains are of three types:
- Public
- Private
- Consortium
31. What is 51% attack?
51% Attack refers to a situation where a group of miners who hold more than 50% of the Network Hash Rate could manipulate with the New transactions (Stopping the transactions to proceed or gaining conformations) or able to reverse the transactions that were recently confirmed and kind of doing Double spend. It is Highly unlikely to be able to do that today but it is possible.
32. What Exactly Do You Know About The Security Of A Block?
Well, a block cannot be modified by all the users on a network. Therefore it offers an excellent level of security. In addition to this, every block is secured using cryptography that is another vote in this matter. Thus one needs not to worry about the safety as well as the security of data that is present in a block.